AI Security and Risk · May 4, 2026
Secure Your Innovator Visa Documents: Torly.ai’s Unified AppSec Monitoring and Remediation
Find out how Torly.ai’s unified AppSec platform integrates SAST, SCA and ASPM to protect and monitor your Innovator Visa documents from code to cloud.

Guarding Your Innovation: A Quick Look at Security Monitoring
Every entrepreneur knows that a killer business plan is only half the battle. The other half? Keeping those prized Innovator Visa documents safe from prying eyes and hidden threats. That’s where unified AppSec security monitoring steps in. Think of it as a digital moat around your castle.
You’ll learn why traditional checks aren’t enough, how modern threats sneak into your code and cloud, and why Torly.ai’s AI-powered defence brings peace of mind. Ready to see your visa docs under iron-clad watch? AI-Powered security monitoring for your Innovator Visa documents
Understanding the Risks: Why Innovator Visa Documents Need AppSec Monitoring
You might trust your solicitor or coach, but code and cloud misconfigurations slip through the cracks. Your pitch deck, financial forecasts and IP blueprints live as files and web apps. Without continuous scrutiny, vulnerabilities can pop up like weeds.
- Phishing attacks targeting your upload portal.
- Malicious dependencies hiding in third-party libraries.
- Unpatched APIs leaving back doors wide open.
Security monitoring catches these as they appear. No more waiting for an audit. Just real-time alerts, guided fixes and audit trails tailor-made for your Innovator Visa journey.
Common Vulnerabilities in Document Handling
Imagine someone tampering with your financial plan minutes before you submit. That’s what happens when document endpoints lack proper access controls. Here’s where gaps occur:
- Insecure uploads via HTTP only.
- Default credentials left unchanged.
- Over-permissive file shares.
A dedicated security monitoring layer spots unauthorised changes. You get notified and can roll back before it’s too late.
GenAI Threats to Sensitive Business Plans
Generative AI helps refine proposals. It also lowers the bar for malicious content injection. Attackers can craft code snippets that blend in, making manual reviews tricky. Continuous security monitoring pairs AI detectors with human insight. The result? Nothing slips through.
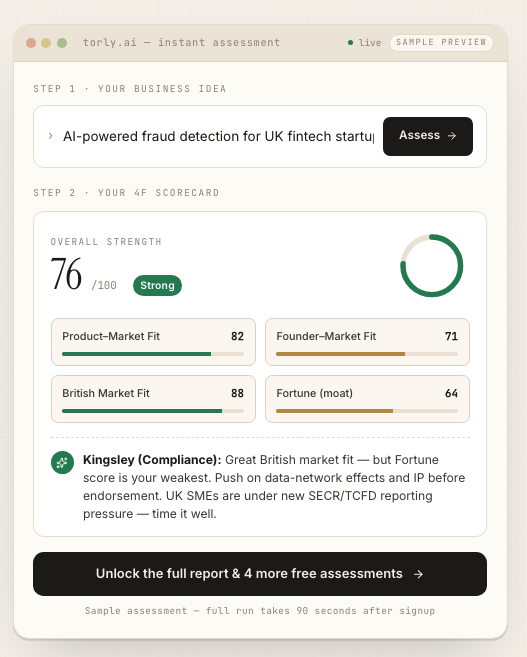
Torly.ai’s Unified AppSec Platform: Three Pillars of Defence
Torly.ai brings together SAST, SCA and ASPM under one dashboard. No more juggling tools. Let’s break down the trio.
Static Application Security Testing (SAST)
SAST scans your codebase for vulnerabilities before deployment. It’s like proofreading your essay for missing references.
- Finds hard-coded secrets in config files.
- Flags risky functions like
eval(). - Enforces coding standards automatically.
Combine SAST with security monitoring and you see threats the moment they are introduced. No blind spots.
Software Composition Analysis (SCA)
Modern apps rely on open-source libraries. A flaw in one dependency can compromise your entire document pipeline.
- Maps all third-party components.
- Checks against known CVEs.
- Recommends secure versions instantly.
With SCA integrated into your security monitoring, you never deploy a vulnerable library again.
Build Your Endorsement Application with 6 AI Agents
Application Security Posture Management (ASPM)
ASPM offers a live view of your entire application landscape. It’s the control centre for your digital assets.
- Tracks misconfigurations in cloud services.
- Monitors user permissions in real time.
- Scores your security posture continuously.
Add proactive security monitoring and you’ll catch drift as soon as someone changes a setting. No more surprises on submission day.
Continuous Monitoring and Remediation: Close the Loop
Security isn’t a one-off task. It’s an ongoing dialogue between code, cloud and compliance. Torly.ai’s AI agents work 24/7 to scan, alert, and guide you through fixes. Here’s why it matters:
- Instant alerts when a new vulnerability emerges.
- AI-driven remediation advice you can act on today.
- Detailed reports for endorsing bodies and Home Office checks.
Stay on top of every change and sleep easy. Stay ahead with 24/7 security monitoring
Practical Steps to Secure Your Visa Documents
You don’t need a PhD in cybersecurity. Follow these six steps:
- Initialise Torly.ai in your repo and cloud.
- Run a baseline security scan.
- Integrate the Torly.ai agent into your CI/CD pipeline.
- Configure real-time alerts for critical events.
- Review daily posture reports.
- Apply recommended patches or configuration tweaks immediately.
By weaving security monitoring into every stage, you ensure your Innovator Visa documents remain untainted and endorsement-ready.
Tips for a Smooth AppSec Journey
- Treat security monitoring as part of your business plan, not an afterthought.
- Involve your team in weekly threat reviews.
- Use Torly.ai’s custom dashboards to track metrics that matter.
- Leverage community insights from Torly.ai forums to stay current.
These small habits compound. Next thing you know, security is second nature.
Conclusion and Next Steps
Innovator Visa applications aren’t just paperwork. They’re your ticket to growth. Don’t leave them exposed to code flaws or cloud missteps. With Torly.ai’s unified AppSec monitoring and remediation, you get:
- Seamless SAST, SCA and ASPM in one place.
- Real-time security monitoring across code and cloud.
- AI guidance to resolve issues fast.
- Detailed audit logs for Home Office endorsement.
Ready for robust security monitoring? Ensure top-tier security monitoring with Torly.ai today