Consulting Services · May 8, 2026
Privacy and Data Security Best Practices for Visa Application Platforms
Explore Torly.ai’s advanced encryption, compliance validation and 24/7 AI support to secure your Innovator Visa documents.

Introduction: Fortifying Your Platform with Visa Application Encryption
Every day, hundreds of entrepreneurs trust online systems to handle their sensitive visa applications. If your platform leaks personal data, you lose credibility, customers and maybe even face hefty fines. That’s why visa application encryption isn’t optional; it’s mission-critical. In this article, we’ll break down privacy and data security best practices for visa application platforms. We’ll show you how to lock down personal files, comply with global regulations and recover quickly if something goes wrong. Ready to secure your Innovator Visa documents with best-in-class encryption? Streamline your visa application encryption with Torly.ai’s AI-Powered UK Innovator Visa Application Assistant.
We’ll cover:
– The main threats to user data.
– Core principles of encryption, in transit and at rest.
– Advanced techniques like end-to-end and zero-knowledge encryption.
– A simple framework for compliance and incident response.
– How Torly.ai’s 24/7 AI support and compliance checks plug into your security stack.
Whether you run a small SME or a global consultancy, these tips will help you build trust while keeping your users’ personal information safe.
Understanding the Risks in Visa Application Platforms
Before diving into encryption, you need to know what you’re up against. Visa platforms process IDs, financials, business plans and health checks. Big prize for cyber criminals.
Personal Data at Stake
When prospects upload their passports and bank statements, that data becomes a prime target. A breach means:
– Identity theft.
– Fraudulent applications.
– Loss of user trust.
– Regulatory fines under GDPR or the UK Data Protection Act.
Common Security Threats
You might think firewalls are enough. They’re not. Watch out for:
– Man-in-the-middle attacks during uploads.
– Insider threats from rogue employees.
– Vulnerabilities in third-party plug-ins or libraries.
– Ransomware locking down your servers.
Core Principles of Visa Application Encryption
Visa application encryption must shroud data both in motion and at rest. Let’s tackle the basics.
Encryption In Transit and At Rest
Encrypt data when it travels over networks and when it’s stored on disks. That means:
– TLS 1.3 for all web traffic.
– Disk encryption with AES-256 or stronger.
– Secure key storage in hardware security modules.
Key Management and Access Controls
Your encryption keys are the crown jewels. If they leak, your vault is open. Best practices include:
– Rotate keys regularly.
– Store keys separately from encrypted data.
– Grant access on a strict need-to-know basis.
– Log every access and audit it often.
Advanced Encryption Techniques
You’ve got basic encryption in place. Time to level up.
End-to-End Encryption for Document Uploads
With end-to-end encryption, only the user and your platform’s decryption service see the raw data. Not your infrastructure team, not a third-party supplier. This approach:
– Thwarts data leaks at rest.
– Helps meet zero-trust models.
– Builds user confidence.
Zero-Knowledge Encryption Models
Zero-knowledge encryption means even you can’t read user documents. It’s a privacy gold standard. How it works:
– Users encrypt files locally.
– Your server only sees ciphertext.
– Decryption keys never leave the user’s device.
Real talk: zero-knowledge adds complexity. But for high-stakes visa application encryption, it’s a game-changer. Well, almost. It’s more like a safety net.
Regulatory Compliance and Global Standards
No one wants fines. Let’s line up with key regulations.
GDPR and UK Data Protection Act
If you process data of EU or UK citizens, you must:
– Provide clear privacy notices.
– Offer data subject rights (access, erasure).
– Report breaches within 72 hours.
– Do impact assessments for risky processing.
Encryption often counts as a mitigating measure. If you demonstrate strong encryption, regulators may lighten penalties.
Navigating International Regulations
Entrepreneurs come from everywhere. You might process data from Canada, Singapore or Australia. That means you need to:
– Map regional requirements.
– Build overlapping controls.
– Keep your policy library up to date.
Implementing a Comprehensive Data Security Framework
Privacy by design isn’t a buzzword; it’s a must. Start with a simple framework.
Data Mapping and Flow Analysis
Know where every bit of data goes. Chart:
– User uploads.
– Third-party transfers.
– Archives and backups.
This map highlights weak points. You can then apply targeted visa application encryption.
Download BP Build Desktop APP for a guided, AI-driven data mapping wizard.
Privacy by Design
Embed privacy at each step. That means:
– Minimal data collection.
– Default settings set to the most private option.
– Regular privacy audits.
Incident Response and Breach Management
Even with the best encryption, breaches can happen. Plan for it:
– Have table-top exercises quarterly.
– Supervise forensic experts immediately.
– Notify regulators, users and partners without delay.
Why Torly.ai Elevates Your Visa Application Security
You already know the theory. How does Torly.ai help?
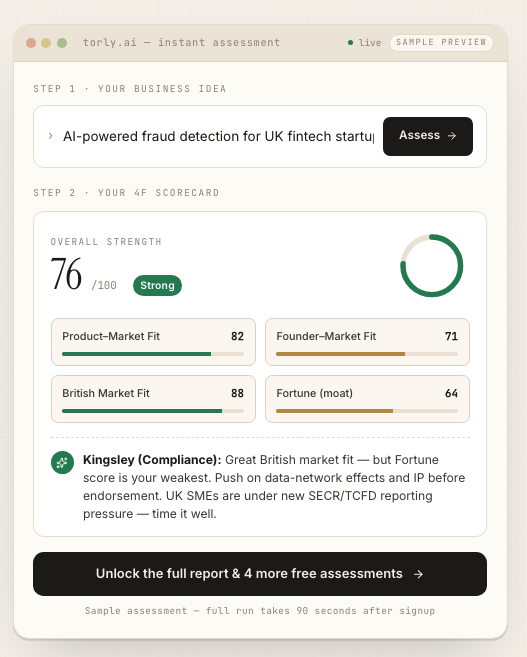
With Torly.ai’s AI-driven agents, you get:
– Automated compliance checks against GDPR and UK Data Protection Act.
– Real-time encryption validation.
– Gap analysis and step-by-step guidance.
– 24/7 AI support that flags unusual activity.
Our platform acts like a virtual security team, ready whenever you need it. No more waiting for office hours. Plus, you’ll see a digital score for your visa application encryption maturity. Spots where you’re strong, spots to improve.
Here’s the kicker: average processing time is 48 hours. So you tighten your security fast.
Your AI-powered assistant for UK Innovator Founder Visa business plan preparation
Case Study: Real-World Impact of Encryption
Imagine a small UK startup preparing its Innovator Visa application. They used standard TLS and at-rest AES. Good start, right? But they missed end-to-end and key rotation. A hacker exploited a misconfigured backup and accessed draft business plans.
After migrating to Torly.ai’s multi-layer encryption and AI-powered compliance checks, they saw:
– Zero data incidents in six months.
– A 30% drop in manual review times.
– Improved confidence when sharing sensitive drafts with endorsing bodies.
At the next funding round, investors cited robust visa application encryption as a key decision factor. Who’d have thought?
Build Your Endorsement Application with 6 AI Agents
Conclusion and Next Steps
Securing your visa application platform is not optional. You need solid visa application encryption at every layer. From data mapping to zero-knowledge models, each practice reduces risk and builds trust. And Torly.ai ties it all together with 24/7 AI-driven support, compliance checks and rapid gap analysis.
Take the next step today. Secure your visa application encryption with our AI-Powered UK Innovator Visa Application Assistant